docker container network configuration
The creation of namespace in Linux kernel
ip netns command
You can complete various operations on the Network Namespace with the help of the ip netns command. The ip netns command comes from the iproute installation package. Generally, the system will install it by default. If not, please install it yourself.
Note: sudo permission is required when the ip netns command modifies the network configuration.
You can complete the operations related to the Network Namespace through the ip netns command. You can view the command help information through the ip netns help:
[root@docker ~]# ip netns help
Usage: ip netns list
ip netns add NAME
ip netns attach NAME PID
ip netns set NAME NETNSID
ip [-all] netns delete [NAME]
ip netns identify [PID]
ip netns pids NAME
ip [-all] netns exec [NAME] cmd ...
ip netns monitor
ip netns list-id [target-nsid POSITIVE-INT] [nsid POSITIVE-INT]
NETNSID := auto | POSITIVE-INT
By default, there is no Network Namespace in the Linux system, so the ip netns list command will not return any information.
Create a Network Namespace
Create a namespace named ns0 through the command:
[root@docker ~]# ip netns list [root@docker ~]# ip netns add ns0 [root@docker ~]# ip netns list ns0
The newly created Network Namespace will appear in the / var/run/netns / directory. If a namespace with the same name already exists, the command will report the error of "Cannot create namespace file" / var/run/netns/ns0 ": File exists.
[root@docker ~]# ls /var/run/netns/ ns0 [root@docker ~]# ip netns add ns0 Cannot create namespace file "/var/run/netns/ns0": File exists
For each Network Namespace, it will have its own independent network card, routing table, ARP table, iptables and other network related resources.
Operation Network Namespace
The ip command provides the ip netns exec subcommand, which can be executed in the corresponding Network Namespace.
View the network card information of the newly created Network Namespace
[root@docker ~]# ip netns exec ns0 ip addr
1: lo: <LOOPBACK> mtu 65536 qdisc noop state DOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
You can see that a lo loopback network card will be created by default in the newly created Network Namespace, and the network card is closed at this time. At this time, if you try to ping the lo loopback network card, you will be prompted that Network is unreachable
[root@docker ~]# ip netns exec ns0 ping 127.0.0.1 connect: Network is unreachable
Enable lo loopback network card with the following command:
[root@docker ~]# ip netns exec ns0 ip link set lo up [root@docker ~]# ip netns exec ns0 ping 127.0.0.1 PING 127.0.0.1 (127.0.0.1) 56(84) bytes of data. 64 bytes from 127.0.0.1: icmp_seq=1 ttl=64 time=0.031 ms 64 bytes from 127.0.0.1: icmp_seq=2 ttl=64 time=0.053 ms 64 bytes from 127.0.0.1: icmp_seq=3 ttl=64 time=0.044 ms
Transfer equipment
We can transfer devices (such as veth) between different network namespaces. Since a device can only belong to one Network Namespace, the device cannot be seen in the Network Namespace after transfer.
Among them, veth devices are transferable devices, while many other devices (such as lo, vxlan, ppp, bridge, etc.) are not transferable.
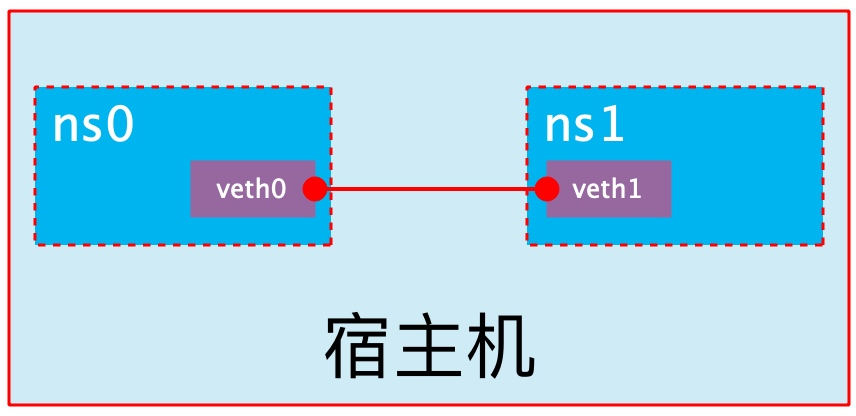
veth pair
The full name of veth pair is Virtual Ethernet Pair. It is a pair of ports. All packets entering from one end of the pair of ports will come out from the other end, and vice versa.
veth pair is introduced to communicate directly in different network namespaces. It can be used to connect two network namespaces directly.
Create veth pair
[root@docker ~]# ip link add type veth
[root@docker ~]# ip a
4: veth0@veth1: <BROADCAST,MULTICAST,M-DOWN> mtu 1500 qdisc noop state DOWN group default qlen 1000
link/ether 16:67:e3:1c:82:c2 brd ff:ff:ff:ff:ff:ff
5: veth1@veth0: <BROADCAST,MULTICAST,M-DOWN> mtu 1500 qdisc noop state DOWN group default qlen 1000
link/ether 82:5d:7e:9d:56:96 brd ff:ff:ff:ff:ff:ff
You can see that a pair of Veth pairs are added to the system to connect the two virtual network cards veth0 and veth1. At this time, the pair of Veth pairs are in the "not enabled" state
Enable communication between network namespaces
Next, we use veth pair to realize the communication between two different network namespaces. Just now, we have created a Network Namespace named ns0. Next, we will create another information Network Namespace named ns1
[root@docker ~]# ip netns add ns1 [root@docker ~]# ip netns list ns1 ns0
Then we add veth0 to ns0 and veth1 to ns1
[root@docker ~]# ip link set veth0 netns ns0 [root@docker ~]# ip link set veth1 netns ns1
Then we configure the ip addresses for these Veth pairs and enable them
[root@docker ~]# ip netns exec ns0 ip link set veth0 up [root@docker ~]# ip netns exec ns0 ip addr add 10.0.0.1/24 dev veth0 [root@docker ~]# ip netns exec ns1 ip link set lo up [root@docker ~]# ip netns exec ns1 ip link set veth1 up [root@docker ~]# ip netns exec ns1 ip addr add 10.0.0.2/24 dev veth1
View the status of this pair of Veth pairs
[root@docker ~]# ip netns exec ns0 ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
4: veth0@if5: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default qlen 1000
link/ether 16:67:e3:1c:82:c2 brd ff:ff:ff:ff:ff:ff link-netns ns1
inet 10.0.0.1/24 scope global veth0
valid_lft forever preferred_lft forever
inet6 fe80::1467:e3ff:fe1c:82c2/64 scope link
valid_lft forever preferred_lft forever
[root@docker ~]# ip netns exec ns1 ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
5: veth1@if4: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default qlen 1000
link/ether 82:5d:7e:9d:56:96 brd ff:ff:ff:ff:ff:ff link-netns ns0
inet 10.0.0.2/24 scope global veth1
valid_lft forever preferred_lft forever
inet6 fe80::805d:7eff:fe9d:5696/64 scope link
valid_lft forever preferred_lft forever
As can be seen from the above, we have successfully enabled this veth pair and assigned the corresponding ip address to each veth device. We try to access the ip address in ns0 in ns1:
[root@docker ~]# ip netns exec ns1 ping 10.0.0.1 PING 10.0.0.1 (10.0.0.1) 56(84) bytes of data. 64 bytes from 10.0.0.1: icmp_seq=1 ttl=64 time=0.068 ms 64 bytes from 10.0.0.1: icmp_seq=2 ttl=64 time=0.039 ms
It can be seen that veth pair successfully realizes the network interaction between two different network namespaces.
veth device rename
[root@docker ~]# ip netns exec ns0 ip link set veth0 down
[root@docker ~]# ip netns exec ns0 ip link set dev veth0 name eth0
[root@docker ~]# ip netns exec ns0 ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
4: eth0@if5: <BROADCAST,MULTICAST> mtu 1500 qdisc noqueue state DOWN group default qlen 1000
link/ether 16:67:e3:1c:82:c2 brd ff:ff:ff:ff:ff:ff link-netns ns1
inet 10.0.0.1/24 scope global eth0
valid_lft forever preferred_lft forever
[root@docker ~]# ip netns exec ns0 ip link set eth0 up
Four network mode configurations
bridge mode configuration
[root@docker ~]# docker run -it --name test1 --rm centos
[root@289c345bb436 /]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
6: eth0@if7: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default
link/ether 02:42:ac:11:00:02 brd ff:ff:ff:ff:ff:ff link-netnsid 0
inet 172.17.0.2/16 brd 172.17.255.255 scope global eth0
valid_lft forever preferred_lft forever
[root@289c345bb436 /]# exit
exit
[root@docker ~]# docker container ls -a
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
# Adding -- network bridge when creating a container has the same effect as not adding -- network option
[root@docker ~]# docker run -it --name test1 --network bridge --rm centos
[root@a828641da65c /]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
8: eth0@if9: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default
link/ether 02:42:ac:11:00:02 brd ff:ff:ff:ff:ff:ff link-netnsid 0
inet 172.17.0.2/16 brd 172.17.255.255 scope global eth0
valid_lft forever preferred_lft forever
[root@a828641da65c /]# exit
exit
none mode configuration
[root@docker ~]# docker run -it --name test1 --network none --rm centos
[root@8240d78b6044 /]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
[root@8240d78b6044 /]# exit
exit
container mode configuration
Start the first container
[root@docker ~]# docker run -it --name test1 --rm centos
[root@680e89b5cb5a /]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
10: eth0@if11: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default
link/ether 02:42:ac:11:00:02 brd ff:ff:ff:ff:ff:ff link-netnsid 0
inet 172.17.0.2/16 brd 172.17.255.255 scope global eth0
valid_lft forever preferred_lft forever
Start the second container
[root@docker ~]# docker run -it --name test2 --rm centos
[root@248fb3005b92 /]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
12: eth0@if13: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default
link/ether 02:42:ac:11:00:03 brd ff:ff:ff:ff:ff:ff link-netnsid 0
inet 172.17.0.3/16 brd 172.17.255.255 scope global eth0
valid_lft forever preferred_lft forever
You can see that the IP address of the container named test2 is 172.17.0.2, which is not the same as the IP address of the first container, that is, there is no shared network. At this time, if we change the startup mode of the second container, we can make the container IP named test2 consistent with the test1 container IP, that is, share the IP, but do not share the file system.
[root@docker ~]# docker run -it --name test2 --rm --network container:test1 centos
[root@680e89b5cb5a /]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
10: eth0@if11: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default
link/ether 02:42:ac:11:00:02 brd ff:ff:ff:ff:ff:ff link-netnsid 0
inet 172.17.0.2/16 brd 172.17.255.255 scope global eth0
valid_lft forever preferred_lft forever
At this point, we create a directory on the test1 container
[root@680e89b5cb5a /]# mkdir /tmp/data [root@680e89b5cb5a /]# ls /tmp/ data ks-script-4luisyla ks-script-o23i7rc2 ks-script-x6ei4wuu
If you check the / tmp directory on the test2 container, you will find that there is no such directory, because the file system is isolated and only shares the network.
Deploy a site on the test2 container
[root@680e89b5cb5a /]# yum -y install httpd [root@680e89b5cb5a /]# echo 'hello world' > /var/www/html/index.html [root@680e89b5cb5a httpd]# ss -antl State Recv-Q Send-Q Local Address:Port Peer Address:Port Process LISTEN 0 128 0.0.0.0:80 0.0.0.0:*
Use the local address on the test1 container to access this site
[root@680e89b5cb5a /]# wget -O - -q 127.0.0.1 hello world
It can be seen that the relationship between containers in container mode is equivalent to two different processes on a host
host mode configuration
Directly indicate that the mode is host when starting the container
[root@docker ~]# docker run -it --name test2 --rm --network host centos
[root@docker /]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UP group default qlen 1000
link/ether 00:0c:29:f2:c3:12 brd ff:ff:ff:ff:ff:ff
inet 192.168.100.110/24 brd 192.168.100.255 scope global noprefixroute ens33
valid_lft forever preferred_lft forever
inet6 fe80::20c:29ff:fef2:c312/64 scope link
valid_lft forever preferred_lft forever
3: docker0: <NO-CARRIER,BROADCAST,MULTICAST,UP> mtu 1500 qdisc noqueue state DOWN group default
link/ether 02:42:3e:aa:88:f4 brd ff:ff:ff:ff:ff:ff
inet 172.17.0.1/16 brd 172.17.255.255 scope global docker0
valid_lft forever preferred_lft forever
inet6 fe80::42:3eff:feaa:88f4/64 scope link
valid_lft forever preferred_lft forever
At this point, if we start an http site in this container, we can directly access the site in this container in the browser with the IP of the host.
Common operations of containers
View the host name of the container
[root@docker ~]# docker run -it --name test1 --rm centos [root@30ae8a5caa62 /]# hostname 30ae8a5caa62
Inject hostname when container starts
[root@docker ~]# docker run -it --name test1 --hostname sunquan --rm centos [root@sunquan /]# hostname sunquan [root@sunquan /]# cat /etc/hosts 127.0.0.1 localhost ::1 localhost ip6-localhost ip6-loopback fe00::0 ip6-localnet ff00::0 ip6-mcastprefix ff02::1 ip6-allnodes ff02::2 ip6-allrouters 172.17.0.2 sunquan # Host name to IP mapping is automatically created when host name is injected [root@sunquan /]# cat /etc/resolv.conf # Generated by NetworkManager nameserver 114.114.114.114 # DNS is also automatically configured as the DNS of the host [root@sunquan /]# ping www.baidu.com PING www.a.shifen.com (36.152.44.96) 56(84) bytes of data. 64 bytes from 36.152.44.96 (36.152.44.96): icmp_seq=1 ttl=127 time=32.8 ms 64 bytes from 36.152.44.96 (36.152.44.96): icmp_seq=2 ttl=127 time=30.2 ms
Manually specify the DNS to be used by the container
[root@docker ~]# docker run -it --name t1 --hostname sunquan --dns 114.114.114.114 --rm centos [root@sunquan /]# cat /etc/resolv.conf nameserver 114.114.114.114
Manually inject the host name to IP address mapping into the / etc/hosts file
[root@docker ~]# docker run -it --name t1 --hostname sunquan --add-host www.a.com:1.1.1.1 --rm centos [root@sunquan /]# cat /etc/hosts 127.0.0.1 localhost ::1 localhost ip6-localhost ip6-loopback fe00::0 ip6-localnet ff00::0 ip6-mcastprefix ff02::1 ip6-allnodes ff02::2 ip6-allrouters 1.1.1.1 www.a.com 172.17.0.2 sunquan
Open container port
When docker run is executed, there is a - p option to map the application ports in the container to the host, so that the external host can access the applications in the container by accessing a port of the host.
-The p option can be used multiple times, and the port it can expose must be the port that the container is actually listening to.
-Use format of p option:
- -p < containerPort >
- Maps the specified container port to a dynamic port at all addresses of the host
- -p < hostPort >:< containerPort >
- Map the container port < containerport > to the specified host port < hostport >
- -p < ip >:< containerPort >
- Map the specified container port < containerport > to the dynamic port specified by the host < IP >
- -p < ip >:< hostPort >:< containerPort >
- Map the specified container port < containerport > to the port < hostport > specified by the host < IP >
Dynamic ports refer to random ports. The specific mapping results can be viewed using the docker port command.
[root@docker ~]# docker run --name web --rm -p 80 nginx
After the above command is executed, it will occupy the front end all the time. Let's open a new terminal connection to see what port 80 of the container is mapped to the host
[root@docker ~]# docker port web 80/tcp -> 0.0.0.0:49153 80/tcp -> :::49153
It can be seen that port 80 of the container is exposed to port 49153 of the host. At this time, we can access this port on the host to see if we can access the sites in the container
[root@docker ~]# curl http://127.0.0.1:49153
<!DOCTYPE html>
<html>
<head>
<title>Welcome to nginx!</title>
<style>
html { color-scheme: light dark; }
body { width: 35em; margin: 0 auto;
font-family: Tahoma, Verdana, Arial, sans-serif; }
</style>
</head>
<body>
<h1>Welcome to nginx!</h1>
<p>If you see this page, the nginx web server is successfully installed and
working. Further configuration is required.</p>
<p>For online documentation and support please refer to
<a href="http://nginx.org/">nginx.org</a>.<br/>
Commercial support is available at
<a href="http://nginx.com/">nginx.com</a>.</p>
<p><em>Thank you for using nginx.</em></p>
</body>
</html>
iptables firewall rules will be generated automatically with the creation of the container and deleted automatically with the deletion of the container.
Maps the container port to a random port of the specified IP
[root@docker ~]# docker run --name web --rm -p 192.168.100.110::80 nginx
View the port mapping on another terminal
[root@docker ~]# docker port web 80/tcp -> 192.168.100.110:49153
Map the container port to the specified port of the host
[root@docker ~]# docker run --name web --rm -p 80:80 nginx
View the port mapping on another terminal
[root@docker ~]# docker port web 80/tcp -> 0.0.0.0:80 80/tcp -> :::80
Network attribute information of custom docker0 Bridge
Official document related configuration
To customize the network attribute information of docker0 bridge, you need to modify the / etc/docker/daemon.json configuration file
[root@docker ~]# vim /etc/docker/daemon.json
{
"bip": "172.17.0.1/24",
"fixed-cidr": "172.17.0.1/25",
"fixed-cidr-v6": "2012:sg6::/64",
"mtu": 1500,
"default-gateway": "10.20.1.1",
"default-gateway-v6": "2012:sg6:abcd::89",
"dns": ["10.20.1.2","10.20.1.3"]
"registry-mirrors": ["https://4nrel0nr.mirror.aliyuncs.com"]
}
The core option is bip, which means bridge ip. It is used to specify the IP address of docker0 bridge itself. Other options can be calculated from this address
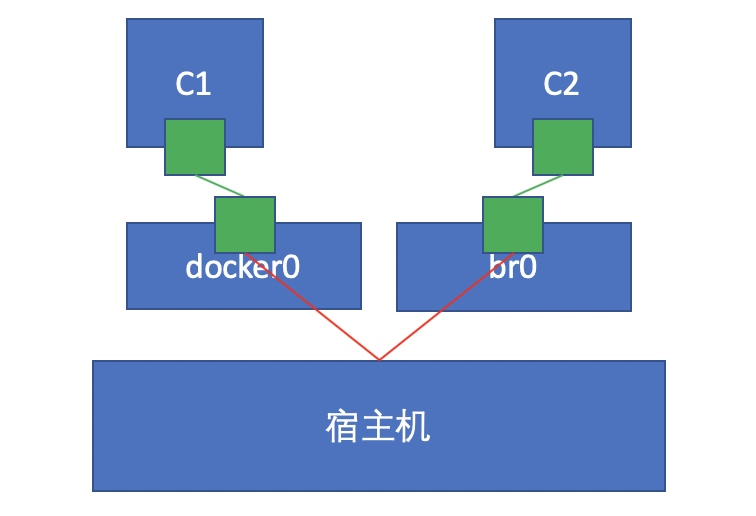
docker create custom bridge
Create an additional custom bridge, which is different from docker0
[root@docker ~]# docker network ls NETWORK ID NAME DRIVER SCOPE edbffc121468 bridge bridge local 065e14687f10 host host local 310212c48eea none null local [root@docker ~]# docker network create -d bridge --subnet "192.168.10.0/24" --gateway "192.168.10.1" br0 a6d7e4f2b7f5b3ee68b5799007ca01192025b04ca0134e552c1e94c2ce9f1d5f [root@docker ~]# docker network ls NETWORK ID NAME DRIVER SCOPE a6d7e4f2b7f5 br0 bridge local edbffc121468 bridge bridge local 065e14687f10 host host local 310212c48eea none null local
Create a container using the newly created custom bridge:
[root@docker ~]# docker run -it --name test1 --network br0 centos
[root@7dfba97c7488 /]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
29: eth0@if30: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default
link/ether 02:42:c0:a8:0a:02 brd ff:ff:ff:ff:ff:ff link-netnsid 0
inet 192.168.10.2/24 brd 192.168.10.255 scope global eth0
valid_lft forever preferred_lft forever
Create another container and use the default bridge:
[root@docker ~]# docker run --name test2 -it centos
[root@5755e759296f /]# ls
bin etc lib lost+found mnt proc run srv tmp var
dev home lib64 media opt root sbin sys usr
[root@5755e759296f /]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
31: eth0@if32: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default
link/ether 02:42:ac:11:00:02 brd ff:ff:ff:ff:ff:ff link-netnsid 0
inet 172.17.0.2/16 brd 172.17.255.255 scope global eth0
valid_lft forever preferred_lft forever
test1 communicates with test2
test1
[root@docker ~]# docker run -it --name test1 --rm --network br0 centos
[root@6f98e4751b0e /]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
33: eth0@if34: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default
link/ether 02:42:c0:a8:0a:02 brd ff:ff:ff:ff:ff:ff link-netnsid 0
inet 192.168.10.2/24 brd 192.168.10.255 scope global eth0
valid_lft forever preferred_lft forever
test2
[root@docker ~]# docker run -it --name test2 --rm centos
[root@fc944d57a62d /]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
35: eth0@if36: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default
link/ether 02:42:ac:11:00:02 brd ff:ff:ff:ff:ff:ff link-netnsid 0
inet 172.17.0.2/16 brd 172.17.255.255 scope global eth0
valid_lft forever preferred_lft forever
Let test2 connect to the br0 network, and one container runs two bridges
[root@docker ~]# docker ps CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES fc944d57a62d centos "/bin/bash" About a minute ago Up About a minute test2 6f98e4751b0e centos "/bin/bash" 2 minutes ago Up 2 minutes test1 [root@docker ~]# docker network connect br0 test2
View the ip information of test2 and try to ping the host test1
[root@fc944d57a62d /]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
35: eth0@if36: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default
link/ether 02:42:ac:11:00:02 brd ff:ff:ff:ff:ff:ff link-netnsid 0
inet 172.17.0.2/16 brd 172.17.255.255 scope global eth0
valid_lft forever preferred_lft forever
37: eth1@if38: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default
link/ether 02:42:c0:a8:0a:03 brd ff:ff:ff:ff:ff:ff link-netnsid 0
inet 192.168.10.3/24 brd 192.168.10.255 scope global eth1
valid_lft forever preferred_lft forever
[root@fc944d57a62d /]# ping 192.168.10.2
PING 192.168.10.2 (192.168.10.2) 56(84) bytes of data.
64 bytes from 192.168.10.2: icmp_seq=1 ttl=64 time=0.094 ms
64 bytes from 192.168.10.2: icmp_seq=2 ttl=64 time=0.121 ms
64 bytes from 192.168.10.2: icmp_seq=3 ttl=64 time=0.095 ms