1, Details of common parameters
This paper is about https://blog.51cto.com/8355320/2471354 The parameter configuration of is extended.
The default configuration file of ansible is / etc/ansible/ansible.cfg. Parameters of ansible can be adjusted in the configuration file, including concurrent thread, user, module path, configuration optimization, etc. common parameters are as follows:
[defaults] inventory = /etc/ansible/hosts Controlled terminal IP Information list; library = /usr/share/my_modules/ Ansible Location of default module; remote_tmp = $HOME/.ansible/tmp Ansible Remote host executes temporary file path; pattern = * Match communication with all hosts; forks = 5 Default number of parallel processes; poll_interval = 15 Default training interval; sudo_user = root sudo Remote host execution user name(Need configuration sudo Jurisdiction); ask_sudo_pass = True Use sudo Whether input is required root Password; ask_pass = True Password required(Configure password free login); transport = smart Transmission mechanism with remote machine; remote_port = 22 Default remote SSH Connection port; module_lang = C The language used for communication between the module and the system; gathering = implicit Control default facts Collect (collect remote host system variable information); roles_path= /etc/ansible/roles Be used for playbook search Ansible roles Route; host_key_checking = False Check the remote host key (it is recommended to shut down); #Sudo_exe = sudo sudo remote command execution; #sudo_flags = -H passes additional parameters of sudo; timeout = 10 SSH Time out; remote_user = root Remote login user name; log_path = /var/log/ansible.log Log file storage path (recommended to open); module_name = command Ansible Command execution default module; #executable = /bin/sh executing Shell environment, user Shell module; #Hash_behavior = replace a specific priority override variable; #Jinja2 extensions allows you to open jinja2 expansion module; #Private key file = / path / to / file private key file storage location; #Display? Skipped? Hosts = true shows the status of any skipped tasks; #system_warnings = True disable the warning of potential problems in running ansible; #"Deprecation" warning = true playbook output disables "not recommended" warning; #Command_warnings = false command module Ansible gives a warning by default; #nocolor = 1 output with color difference, on / off: 0 / 1; pipelining = False open pipe SSH Channel optimization; [accelerate] accelerate Cache acceleration. accelerate_port = 5099 accelerate_timeout = 30 accelerate_connect_timeout = 5.0 accelerate_daemon_timeout = 30 accelerate_multi_key = yes
2, Ansible performance tuning
The specific optimization methods are as follows:
(1) Ansible SSH shutdown key detection
By default, when you log in to the remote client server with SSH, you will check the public key of the remote host and record the public key of the host in the ~ /. SSH / known hosts file. The next time you visit the same host, OpenSSH will check the public key. If the public key is different, OpenSSH will issue a warning. If the public key is the same, you will be prompted for the password.
SSH checks the public_key of the host according to the StrictHostKeyChecking variable. The StrictHostKeyChecking check levels include: no (no check), ask (ask), yes (check every time), False (close check).
The following code is added to Ansible configuration file to close the StrictHostKeyChecking check check:
Configuration content host_key_checking = False
(2) OpenSSH connection optimization
When using OpenSSH service, the default server-side configuration file UseDNS=YES status. This option will cause the server to perform DNS PTR reverse resolution according to the IP address of the client, get the host name of the client, then query the DNS forward A record according to the acquired host name, and verify whether the IP is consistent with the original IP. Turn off DNS resolution code as follows:
Operation instruction sed -i '/^GSSAPI/s/yes/no/g;/UseDNS/d;/Protocol/aUseDNS no' /etc/ssh/sshd_config /etc/init.d/sshd restart
(3) SSH pipelining accelerates Ansible
SSH pipelining is a simple way to speed up the execution of Ansible. SSH pipelining is turned off by default, which is to be compatible with different sudo configurations, mainly the required option.
If you do not use Sudo's recommendation to turn on this option, turning on this option can reduce the number of SSH connections to perform tasks on the controlled machine when Ansible performs no file transfer. When using Sudo operations, you must disable the requirement option in the configuration file / etc/sudoers on all managed hosts.
Operation instruction sed -i '/^pipelining/s/False/True/g' /etc/ansible/ansible.cfg
(4) Ansible Facts cache optimization
During the execution of ansible playbook, Gather facts will be executed by default. If you don't need to get the client's fact data, you can turn off the function of getting fact data. After turning off, you can speed up the execution efficiency of ansible playbook. To turn off the fact function, add the following code to the playbook yaml file:
Code content gather_facts: no
Ansible facts component is mainly used to collect basic static information of client devices, which can be easily referenced in configuration management. Facts information is directly referenced as Ansible Playbook variable information. We can customize facts to collect the information we want. At the same time, we can expand facts information through factor and Ohai, or store facts information in Redis cache. The following steps are the steps for facts to use Redis cache.
1. Deploy Redis service
[root@ansible~]# yum -y install gcc gcc-c++ [root@ansible~]# cd /usr/local/src [root@ansible~src]# wget http://download.redis.io/releases/redis-4.0.2.tar.gz [root@ansible~src]# tar -zxvf redis-4.0.2.tar.gz [root@ansible~src]# cd redis-4.0.2 [root@ansible~redis-4.0.2]# make MALLOC=libc [root@ansible~redis-4.0.2]# cd src [root@ansible~src]# make install PREFIX=/usr/local/redis/ [root@ansible~src]# cp redis.conf /usr/local/redis/ [root@ansible~src]# vi /etc/profile export PATH=/usr/local/redis/bin:$PATH [root@ansible~src]# source /etc/profile //Command to start and stop Redis service: [root@ansible~src]# nohup /usr/local/redis/bin/redis-server /usr/local/redis/redis.conf &
2. Install Python Redis module
Installation instructions [root@ansible~]# easy_install pip [root@ansible~]# pip install redis
3. Ansible integrated Redis configuration
Add code in the defaluts section of the configuration file / etc/ansible/ansible.cfg. If the redis password is admin, open the admin password line:
The code is as follows [root@ansible~]# /etc/ansible/ansible.cfg gathering = smart fact_caching = redis fact_caching_timeout = 86400 fact_caching_connection = localhost:6379 #fact_caching_connection = localhost:6379:0:admin
4. Test Redis cache
Ansible playbook executes nginx.yaml script file, as shown in the figure:
ansible-playbook nginx.yaml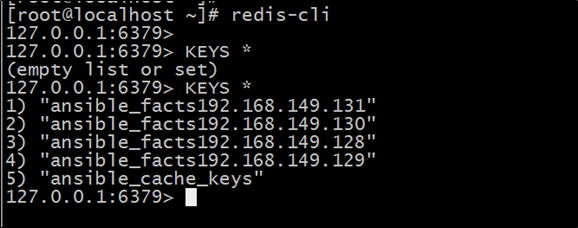
(5) ControlPersist SSH optimization
The ControlPersist feature requires higher version SSH support. CentOS 6 does not support it by default. If you need to use it, you need to upgrade Openssh yourself.
ControlPersist is a persistent Socket, which verifies multiple communications at a time. Only SSH client configuration needs to be modified, that is, Ansible is managed by the host.
You can use YUM or source code compilation to upgrade the OpenSSH service. After upgrading, you can set ControlPersist as follows. Create a config file in the user's home directory. If ansible logs in to the client as root, add the following code to the / root/.ssh/conf file of the client:
Code content Host * Compression yes ServerAliveInterval 60 ServerAliveCountMax 5 ControlMaster auto ControlPath ~/.ssh/sockets/%r@%h-%p ControlPersist 4h
After the ControlPersist feature is enabled, SSH saves the time of each verification and creation after the sockets are established, and the execution speed of Ansible is greatly improved.